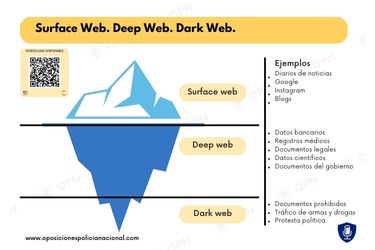
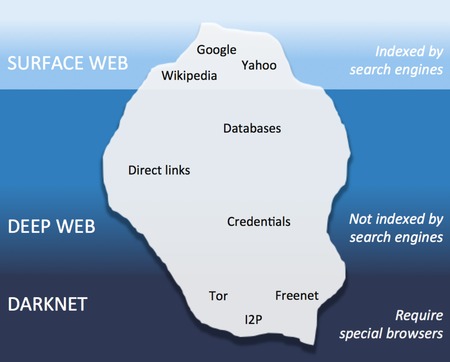
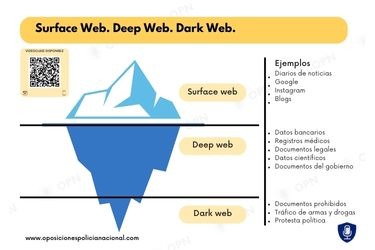
This enables the fetching of responses to queries sent by you and me. Simply put, search engines use software (called crawlers or web spiders) that visit all sites and send them for indexing. If a particular website does not allow the crawlers to send the data for indexing, the site is not indexed and hence, cannot be seen on search engines.
It is composed of “non-indexed” content that is unreachable by the web crawlers used by Google, Bing, and other search engines to find and link pages. The legal issues arise not from the access, but from the activities conducted within these hidden networks. For example, browsing a whistleblower platform or reading censored news through a Tor mirror site is lawful in many places and can even serve democratic and journalistic interests. The “onion routing” technology underpinning the dark web was developed by researchers at the U.S.
Standard Chartered’s Alvaro Garrido On AI Threats And What CIOs/CISOs Must Know In Their AI Journey
However, the deep web can also host illegal content such as pirated media. Anyone can access this material without needing a different web browser such as Tor. Many websites on the deep web avoid showing up in search engine results by blocking the bots that ‘crawl’ the internet to collect information for search engine indexes. Theoretically speaking, it should be impossible to locate dark web servers and track visitors. However, in practice, security flaws in Tor and incorrect server configurations can expose this information to those interested in accessing it. The deep web is a section of the internet that cannot be indexed by web crawlers.

To discover content on the web, search engines use web crawlers that follow hyperlinks through known protocol virtual port numbers. This technique is ideal for discovering content on the surface web but is often ineffective at finding deep web content. It is also worth mentioning that it is believed that the NSA hosts a large number of entry and exit nodes into the dark web. The good news is that there is a much faster version of privacy technology that is similar to Tor, albeit much faster. A VPN is a technology that (like Tor) provides you with a string layer of encryption to stop local networks, ISPs, and government agencies from being able to monitor your online activities. To access the purposely hidden part of the internet, you have to use special tools such as the Tor browser.
What Is Surface Web Or Indexed Web?
Any online activity can carry breadcrumbs to your identity if someone digs far enough. The dark web was once the province of hackers, law enforcement officers, and cybercriminals. However, new technology like encryption and the anonymization browser software, Tor, now makes it possible for anyone to dive dark if they’re interested. The dark web has numerous legitimate uses but is still home to various criminal activities. Conversely, the deep web is a regular part of the online experience for almost every internet user.
What Is Cyber Threat Intelligence?
This is because the dark web is placed on darknets, an overlay network that exists ‘on top of” the regular internet. Unlike the dark web, which is deliberately obscured by layers of technology, the deep web exists just below the surface web. The majority of the deep web consists of regular websites that require users to create an account before they can be accessed. The dark web is a subsection of the deep web including websites that one can only access through purpose-built web browsers.
First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. If something cannot be found, even if it can be opened, then it too belongs to the deep web. If you configure Facebook to hide your profile from search engines, for example, then even if a search bot gets to it, it will have to ignore it. Nor can a search engine process content that a Web page generates only when the page is opened and that varies depending on who opens it.
How To Delete Yahoo Account In 2025
- In this case, two familiar people communicate with each other directly over the internet.
- You may already be aware that malicious actors can use these to harm your credit, engage in financial theft, and breach of your other online accounts.
- Obviously, the search engines won’t be opting for a monthly subscription to index the catalog of such websites.
- TOR also lets users connect to websites in the surface and deep web anonymously, to prevent internet service providers from seeing what they are browsing.
- While law enforcement agencies around the world actively monitor these platforms and conduct coordinated takedowns, new marketplaces often re-emerge under different names or infrastructures.
It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. The dark web is a very popular platform for journalists, political bloggers and political news publishers, and in particular, those living in countries where censorship shields most of the internet. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. For example, the deep web is often a platform used by political activists who own a blog.
How To Access The Dark Web Or Deep Web Using Tor
Did you login to your eBay account to send a message about a parcel? The dark web’s infrastructure serves those needing privacy, including activists, whistleblowers, political dissidents, and even regular citizens attempting to escape censorship or persecution. Below, we’ve included an explanation of the deep and dark web and their differences.
LostMyPassword – Dual Use Password Recovery And Credential Dumping Tool
One must always respect the laws and regulations regarding privacy. The deep web resides just beneath the surface web, and it comprises content and services largely inaccessible to regular internet users. Though some content and services on the deep web are obscured through non-indexing, the majority are hidden through paywalling and password protection. Most of the deep web’s content and services are accessible via regular web browsers. The dark web is a hidden segment of the internet that isn’t indexed by standard search engines. It lives inside encrypted networks like Tor and I2P, allowing users and site operators to remain anonymous.
Most activities on the deep web are legal and intended to protect user privacy. One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons.
She holds a Bachelor’s degree in Liberal Arts and a triple Master’s degree in Literary and Cultural Studies. Outside of work, she is a travel enthusiast, music lover and avid learner interested in global cultures, spirituality, psychology and neuroscience. Its secure protocols and encryption ensure that even if your traffic passes through a compromised node, the authorities can’t trace any activity back to you. It even has a dark web monitor to notify you in case your data gets leaked on the dark web. Dark web risks emanate from the vulnerabilities of its underlying technology — the Tor network. If malicious actors operate an exit node, they can infect your traffic or downloads with worms, trojans or keyloggers.
Risks Of Accessing The Deep Web Vs The Dark Web
Many dark websites can be reached by specialized search engines designed for that purpose, but not by standard search engines. In order to access these search engines and sites, it is necessary to use specific browsers, such as the Tor Browser. The dark web allows legitimate users to avoid censorship, but it also creates opportunities for cybercrime. Darkweb (or dark net) is a relatively small part of the deepweb but contains highly secured and inaccessible data from search engines as well as standard browsers. In the darkweb, users can communicate and conduct business anonymously.
In fact, it can be argued that the closure of Silk Road and the subsequent arrest and conviction of Ross Ulbricht, its founder, only heightened interest in darknets and their illegal wares. Sociologist Isak Ladegaard, who built an algorithm to monitor sales data on Silk Road-type marketplaces, declared that all the media coverage boosted people’s awareness of the existence of the dark web. The dark web hosts all kinds of illegal activities, many of which are the buying and selling of firearms, drugs, counterfeit money, fake passports, and stolen accounts. Sections of the dark web are often closed down too, as part of police operations. However, there are plenty of legal and legitimate online activities that require privacy and anonymity.
Given its anonymous nature, the dark web is also used for illicit and even illegal purposes. These include the buying and selling of illegal drugs, weapons, passwords, and stolen identities, as well as the trading of illegal pornography and other potentially harmful materials. Several sites hosting illegal material have been discovered by government agencies and shut down in recent years, including Silk Road, AlphaBay, and Hansa. The dark web’s anonymity has also led to cybersecurity threats and various data breaches over the last few decades. However, while visiting the dark web itself isn’t against the law, engaging in illegal activities there is.


