You can check out this guide on the best antivirus software applications today. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
Deep Web Guide: Getting There & How It Differs From The Dark Web
Valentina Bravo is an editor at Cloudwards with a rich background in technology topics, particularly productivity tools and online security. She holds a Bachelor’s degree in Liberal Arts and a triple Master’s degree in Literary and Cultural Studies. Outside of work, she is a travel enthusiast, music lover and avid learner interested in global cultures, spirituality, psychology and neuroscience. The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity. Read our comprehensive “what is the dark web” guide to understand how it works and the risks and benefits.
Malware and scams are scattered like landmines around the dark web. And with many unfamiliar-looking sites on the dark web, it’s harder to distinguish safe websites from shady ones, and easier to fall victim. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance. While strong encryption, VPNs, proxy servers, and hidden web addresses can all contribute to a more anonymized experience, there is no singular system available that is completely private and secure.

Top 10 Best Dark Web Search Engines In 2025 Safe &
I2P must be downloaded and installed, after which configuration is done through the router console. Then individual applications must each be separately configured to work with I2P. You’ll need to configure your browser’s proxy settings to use the correct port on a web browser.
Install Premium Antivirus Software On Your Phone
The inherent advantage of unindexed content becomes apparent in the preservation of privacy. Users cannot access a dark web marketplace without the Tor browser. And while it’s based on the Mozilla Firefox browser, Tor is not as well maintained and has page rendering issues.

Why Can’t I Access Onion Sites?
It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading. As long as there’s a demand for the ability to privately browse the internet and, more importantly, host websites anonymously, the deep web will exist.
Why Use The Tor Browser With A VPN

What should you do if your information is found in a data breach or you think it’s been leaked somewhere? Change your passwords and watch out for suspicious activity on your credit reports. You can access the dark web on mobile with a dedicated dark web browser app. Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing. Dark web domains tend to be inconsistent — new ones pop up and others disappear, which makes sense if they offer questionable or illegal goods and services. To explain what webpages are on the Deep Web, it will help to first understand a bit about how search engines work.
Moreover, you need to be more cautious while accessing it, as without proper safety, you can fall into the wrong hands and face serious consequences. Following are important tips you need to remember while visiting this dark part of the web. Freenet isn’t just an anonymity tool—it’s practically a digital manifesto. This peer-to-peer (P2P) platform encrypts data before sharing it and operates on a fully decentralized and distributed network.
Meanwhile, cybersecurity experts monitor the dark web, scanning for stolen data and emerging threats. If your information surfaces in these murky depths, there’s very little you can do – but knowing the risks involved is a first step toward defence. This internet space can be dangerous but you can safely get on it by using a VPN and then connecting to Tor. Our experience has shown that this is the #1 way of doing things without risking your privacy.
How To Get On The Dark Web Safely & Anonymously In 2025?
First, most of the content on the dark web is highly illegal, and no matter the precautions are taken to stay anonymous, you should be aware that you enter the dark web world at your own risk. It doesn’t use the Tor network, so it’s not ideal for accessing the dark web, but it’s perfect for anyone looking to maintain strong privacy without needing to configure a thing. As part of the GNU Project, GNUnet is fully aligned with free software principles and a strong focus on privacy.
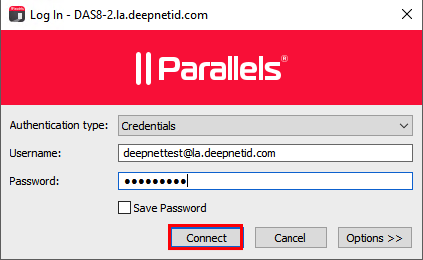
- The dashboard should open properly, indicating you’re ready to connect to any VPN server.
- Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki.
- It’s one of the most well-known secret search engines on the dark web.
- There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes.

Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries. Did you know that Google only shows you a glimpse of all the websites that actually exist? The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search. Use VPN, avoid logging into personal accounts, enable Tor security settings, and stick to trusted sites.
More Ways To Stay Safe On The Dark Web
We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites. And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing. Ruheni Mathenge specializes in writing long-form content dedicated to helping individuals and businesses navigate and understand the constantly evolving online security and web freedom worlds.
With Tor Browser, you are free to access sites your home network may have blocked. Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions.

DuckDuckGo offers an .onion version of its search engine, while Sci-Hub offers access to millions of scientific articles and papers. Library Genesis offers a search engine for collections of books on such topics as computers, business, technology, and more. These are only a few of the .onion search engines that are available. Connecting to the Tor network might raise eyebrows depending on who and where you are. Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor.
There are several programs that hackers frequently use on the dark web. On top of that, the installation process of Freenet is rather easy. Simply download the file, install the software, and you’re ready to use its web-based interface. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. The advantages of I2P are based on a much faster and more reliable network.