The Directory of Open Access Journals is a deep internet search engine that provides access to academic papers. The deep web is made up of content that typically requires some form of accreditation to access. Examples include library databases, email inboxes, personal records (financial, academic, health, and legal), cloud storage drives, and company intranets. If you have the correct details, you can access the content through a regular web browser. It is the part where we use search engines like Google and includes all the indexed websites and pages. Although the Tor browser protects your online privacy using a reliable VPN at the same time is a plus.
Engaging with the dark web securely requires preparation, awareness, and the right tools. Here are some of the ways to reduce the risks that come with using the dark web. As we enter 2025, these tools are adapting with improved security and functionality to meet user needs. It’s a lesser-known but highly effective unrestricted search engine ideal for in-depth exploration.

Features Of Torch
Recon allows users to search for specific products from dark web vendors and marketplaces as opposed to just the sites themselves. Haystak is one of the most comprehensive dark web search engines, with a search library of more than 1.5 billion pages. It has a freemium model with ads, and a paid version for ad-free browsing and extra features. Torch is probably the most well-known dark web search engine, and it is also one of the oldest.
- This makes it even harder for third parties to see your email traffic.
- That means website operators and third parties can’t track your online activity when you use Torch.
- Yes, the Hidden Wiki remains one of the most accessed community-curated directories for .onion links, though users must verify each link’s authenticity.
- Boasting an extensive archive of over 400,000 pages, Torch excels in navigating the depths of the Dark Web, consistently providing relevant results for a wide array of search queries.
- After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
How Can You Monitor The Dark Web Without Using Search Engines?
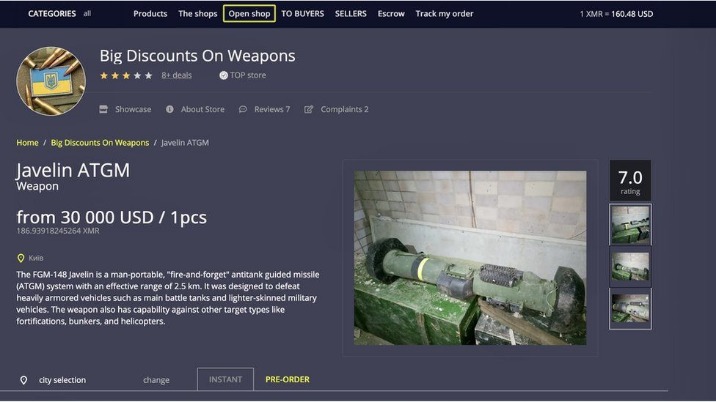
This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web. Darknet markets facilitate transactions for illegal goods and services. Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources.
How To Turn Off SafeSearch On Google, Bing, DuckDuckGo, Yahoo
Visit a known .onion site (e.g., Ahmia’s .onion link) to ensure Tor is working. These tools are the dark web’s rogue librarians, mapping a realm where traditional rules don’t apply. They lack the scale or polish of surface web engines but are critical for exploring what’s deliberately hidden.
However, time has changed, and now several services offer free dark web access with the least amount of technical knowledge. The dark web is a mysterious place that can only be accessed with specific tools and services. Install Norton VPN to encrypt your internet connection and help protect the data you share online. Use community-trusted directories, forums, and check reputation scores or comments on Reddit/darknet forums. Haystak has a free version but also offers a premium version with advanced features and deeper indexing.
Don’t Provide Personal Information
They differ in search results, depending on which sites their crawlers index, as well as in advanced search capabilities, such as Boolean operators or multilingual support. Some are built for general discovery, while others focus on specific types of content. For investigators, using multiple search engines and comparing results is key to a thorough investigation. Targeting searches to engines that specialise in certain areas can also improve efficiency and accuracy. There are a lot of great resources that explain what the dark web is, where it originated from and the nefarious activity that occurs there on a daily basis. This article is focused on identifying safe access options and then the multiple search options available using freely available dark web search engines that crawl the dark web.
Haystak: The Premium Powerhouse For Deep Dives
Over half of its listings pose potential risks to individuals and organizations. To counter this, dark web monitoring has become essential to detect these threats and safeguard digital privacy. Now equipped with an overview of these essential dark web search engines, you’re ready to conduct your own searches confidently and securely.
What Are Onion Sites?
- Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling.
- Torch is one of the oldest and most well-known darknet search engines.
- The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
- That means that only 0.024% of all the known pages are findable in Google’s search engine.
- The Tor network adds a layer of anonymity, which helps dark web sites remain hidden and makes it impossible for conventional search engines to index them.
But that doesn’t mean your dark web activity is completely anonymous. Before you start browsing websites on the dark web, make sure to protect yourself by using a VPN, proxy, or Tor. Search engines are integral to the web browsing experience, but only about 10% of all websites are indexed on a typical search engine.
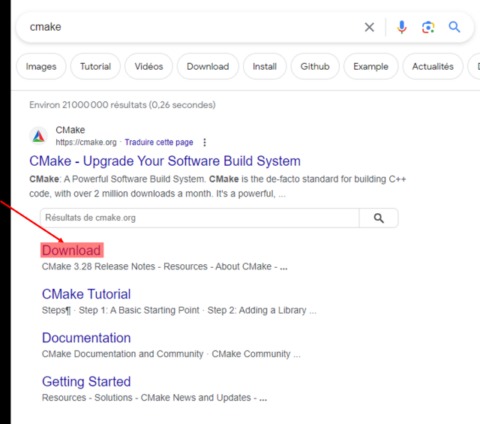
DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. In 2025, as privacy battles intensify, these tools are more vital than ever.
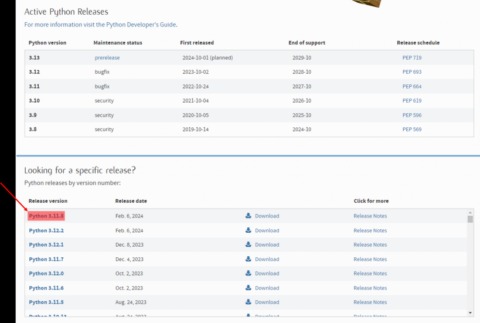
Regular system audits and avoiding executable files further reduce infection risks. While Tor provides strong anonymity, activity can potentially be traced through advanced techniques like timing attacks, exit node monitoring, or vulnerabilities in engine setups. Yes, access is possible via Tor’s official Android app or Onion Browser for iOS, allowing searches on engines like OnionLand, which offers mobile-friendly designs. In 2025, use APIs (e.g., Ahmia’s) for automated OSINT, but employ sandboxing and ethical guidelines to avoid risks like malware or legal issues while analyzing trends.

Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays. Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content.
OnionDir: The Clear Net Directory Of Tor Onion Sites
Always run the latest version of the Tor Browser to protect against security vulnerabilities. Outdated versions may contain weaknesses that attackers can exploit to compromise your anonymity. I recommend enabling automatic updates and checking for new versions before each session. SecureDrop stands out as the leading platform for secure document sharing used by major news organizations. This open-source whistleblowing system enables anonymous file transfers with strong encryption.
Start with verified directories like Ahmia or Hidden Wiki, use a secure environment (VM + VPN + Tor), and stick to ethical, research-oriented content only. The surface web is publicly indexed, the deep web requires login or credentials, and the dark web is intentionally hidden and accessed via Tor or I2P. ZeroBin is an encrypted paste tool on the dark web, often used for sharing messages or files without storing user data. LeakLooker indexes live and historical data leaks found on underground forums, often used to identify early data breach activity. Use a VPN, access the dark web only through the Tor browser, avoid logging in with personal credentials, and use virtual machines for isolation.