Notably, cryptocurrency has become a valid option for carding operations, whether through exploiting stolen crypto wallets and accounts or using stolen credit card details to purchase cryptocurrency. With this stolen information, fraudsters can make unauthorized purchases, withdraw funds, or even create counterfeit credit cards. The risks are real, as victims can face significant financial losses, damage to their credit scores, and potential identity theft. It’s important to detect fraud when a threat actor is trying to use stolen payment information to make a purchase from your business.
Protecting Yourself From Credit Card Fraud On The Dark Web
- Learn the basics of credit card cards, including features, fees, and rewards to make informed decisions about your credit card usage.
- After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces.
- These cards can be used to make purchases online or in-store, and can even be used to withdraw cash from ATMs.
- Dark web credit card fraud poses serious risks to consumers and businesses alike.
- Businesses pass fraud-related costs on to consumers through higher prices.
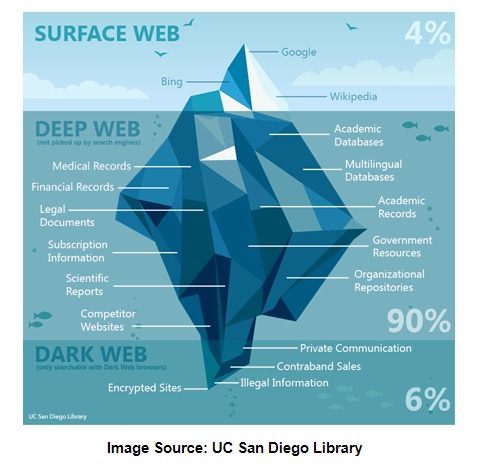
When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces. These black markets allow buyers and sellers to make anonymous transactions using a combination of encrypted messages, aliases, and cryptocurrency. Discover the pros and cons of using credit cards or card for purchases, including benefits and risks, to make informed financial decisions. Dark web credit cards are often sold on online marketplaces, which can be accessed through specialized browsers like Tor.
Visa, the biggest U.S. card company, accounted for more than half (913,955) of all the stolen U.S. cards, followed by Mastercard (406,851) and American Express (143,836), the release from NordVPN said. Visa prepaid cards were twice as likely to be found on the dark web as the company’s introductory level credit cards. Understanding the Dark Web is crucial for detecting potential threats and taking necessary precautions to protect your credit card information. The impact of dark web credit card fraud extends far beyond individual card holders. Stolen credit cards are also harmful to the businesses from which they were stolen in the first place. Customers whose payment information was stolen are less likely to want to continue doing business with your organization after a hack and your organization may sustain long-lasting reputational damage.
1 Next, we’ll look at how this sensitive data ends up for sale online. With stolen payment cards, a cybercriminal can immediately make purchases under your name, or even drain your bank account. And what’s worse, this shady corner of the internet is only getting bigger. Most of use just have the standard personal account, but Premier and Business accounts also exist, and are up for sale on the dark web. But those tiers don’t have much influence on dark web prices, which are largely governed by account balance.
More From Moneycom:
The Dark Web is a hidden part of the internet that can only be accessed through specialized software. It operates beyond the reach of normal search engines and is known for its anonymity. Criminals take advantage of this anonymity to carry out illegal activities, including the buying and selling of stolen credit card information. On the Dark Web, hackers and fraudsters can find a wide array of resources to exploit credit card data, such as sale platforms and forums. Legitimate users of the dark web include activists, or people who live under oppressive regimes, but they only account for a small percentage of the dark web.
Social Media Data
Join us as we break down and discover the methodologies of card fraud using our dark web monitoring tool, Lunar. However, the validity of the data hasn’t been confirmed yet, so it could very well be auto-generated fake entries that don’t correspond to real cards. Prices can vary based on demand, how complete the data is and how easily it can be monetized by criminals. Here is a detailed description of how scammers steal information from the credit card dark web. It has a bidding feature, with new batches of stolen data being frequently added. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily.
Read More On Hackers And Cybercrime Prevention
The proceeds from sales of card numbers are used for enabling organized crime and gang activities, weapons exchange, trafficking drugs and guns, and many other illegal activities, he says. Unlike carding shops, which primarily focus on the trade of information, carding forums serve a broader purpose within the cybercriminal community. On these forums, actors will often share techniques, hacking tools, strategies, and resources for conducting fraudulent activities. This stolen information is exploited by threat actors for financial gain through unauthorized charges, account takeover, and identity theft. The resulting financial loss is tremendous not only for the individual victim but also for the financial provider and any involved organizations.
Tools And Services For Detection
Over the years several advanced tools have been developed to help track and prevent such fraudulent activities. In addition to these types of listings, there are other free tools usually available on credit card sites. These tools include for example different types of checkers, which assist threat actors in verifying whether the stolen card information they possess is valid and can be used to make unauthorized purchases. Dark web credit cards are standard, but you don’t have to fall victim to stolen credit cards.

Customers Who Read This Book Also Read
Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar. These stolen cards have value because they can be used to purchase high-value items or gift cards, which can then be resold for cash.

To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. Contrary to popular belief, most carding platforms no longer hide in the dark web (i.e. the Tor network). The sites I’ve evaluated this year all had clear web addresses—with ‘.onion’ versions available for some of them. This enables systems to detect fraud based on minute changes in transaction velocity, merchant category patterns, and even the time of day purchases are made. Financial institutions tighten their security measures to prevent fraud but that also prevents legitimate transactions as a result.
Indicators Of Compromise In Threat Intelligence
Not only can you buy a hacked social media account via the dark web, but you can also buy likes and followers for next to nothing. This is unsurprising, given the amount of social media profiles with high follower counts yet low engagement. As an Ex-undercover Cop, now Private Investigator, I make sure that you have the right information for the right reason under the right circumstances. With extensive knowledge using law enforcement databases and the internet, I find the information you are looking for with speed, accuracy, and the necessary discretion to achieve the desired results.
- Internet criminals buy and sell personal data on the dark web to commit fraud.
- It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures.
- You could receive an email or a message from what might look like a legitimate company, such as an online retailer or bank, but it is a fraudster.
- Prices can vary based on demand, how complete the data is and how easily it can be monetized by criminals.
- When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces.
- One of the most recent and devastating cyberthreats facing merchants is the rise of Magecart hackers, according to Mador.
From Social Security numbers to bank logins and medical records, cybercriminals buy and sell stolen data every day. Accounts with higher balances are more expensive, as they provide a greater potential payoff for attackers. Banks that are preferred targets often have weaker security measures or systems allowing quick transfers. US banks and international institutions with lenient fraud detection systems are particularly popular. Additionally, attackers favor accounts from banks that have high transaction or withdrawal limits. As per Cybersixgill’s “Underground Financial Fraud H report,” more than 4.5 million dark web credit cards were up for sale during the first half of 2022.