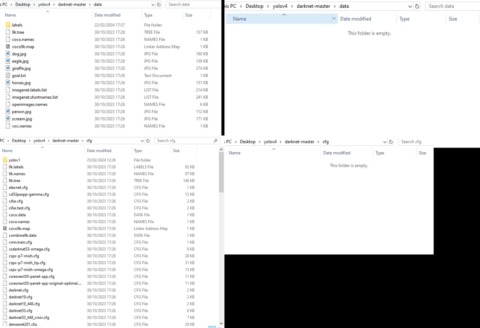
At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays.
The line between privacy and peril is often one of intent—and operational discipline. Accessing Tor is not banned, but authorities aggressively prosecute darknet commerce under broad drug and extremism articles. Belarus requires VPN providers to register with the government, and unregistered use can trigger administrative fines.
Relay Roles And End‑to‑End Encryption
- The term is very general, as there are actually a number of ‘darknets’ available such as ‘Freenet’ and ‘I2P’ but the TOR network has become the most popular.
- A VPN also masks your online behavior from ISPs, which could flag you as suspicious for accessing the dark web.
- This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing).
- In August 2021, co‑founder “DeSnake” relaunched AlphaBay with a decentralized infrastructure and stricter vendor vetting.
- Internet shutdowns affected 4.78 billion people in 2024 alone, as governments from Iran to Myanmar throttled access during protests and elections.
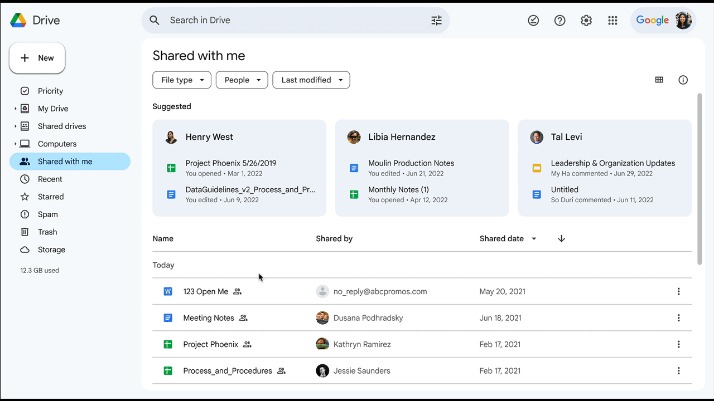
This engine uses information from publicly sourced sites (such as Wikipedia) with the aim of increasing traditional results and improving relevance. Its philosophy emphasizes privacy and not registering user information. You won’t be able to search the dark web with a regular browser (such as Chrome or Firefox). Besides, your online activity on such browsers is visible to your ISP unless you connect to a VPN service.
How To Access The Dark Web Safely Using Tor
You should also consider freezing your credit to prevent identity theft. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details.
How Do I Browse Onion Sites Safely?
Each wave of takedowns disrupted marketplaces but also pushed criminals toward more resilient, decentralized models. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action. While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams.
What To Do If You See Something Illegal
The core functionality of the dark web relies on onion routing, a method that encrypts and routes user communications across multiple servers, known as nodes. It indexes a wide array of content, including both legal and illegal sites. Unlike the regular internet, the Tor network can’t be accessed via standard browsers. Once you have the Tor Browser installed, launch it and click “Connect.” That’s it! Keep in mind that because Tor encrypts your traffic, your internet speeds may be slower than usual. But rest assured that your privacy and security are well worth the trade-off.
Best Dark Web Websites: Video
Accessing blocked content can result in being placed on a watch list or imprisonment. Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal.
Marketplaces For Everything Illegal
For instance, I wanted to know Twitter’s onion URL, a very simple piece of information. Yet, it reported everything but that showing how far these search engines have to go in order to improve. We continuously monitor and update our directories to minimize risks and ensure users have access to trusted, legitimate sites. Our goal is to empower you with reliable information and resources, making your dark web experience as secure and informed as possible. Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline.
To safely use the Hidden Wiki, verifying the authenticity of links is essential. First, rely on community-vetted sources and updated link lists from trusted forums like Dread or The Hub, where users report scams and share verified onion addresses. Check for recent user reviews or feedback to ensure the site is still operational and legitimate. Always use PGP keys when available to verify the identity of marketplaces or services. Another good practice is to cross-reference links with multiple sources to confirm consistency. Avoid clicking on links posted in random or unmoderated sections, as these are often the most dangerous.
How To Use Tor, And Is It Safe To Access The Dark Web?

If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust.

Tor websites may provide secure access to cryptocurrency wallets and anonymous email clients, and they’re also used to access black market sites. In the image above, (a) is the surface web, which includes publicly visible websites like blogs, shopping sites, and news sites. (b) is the deep web, which consists of sites that require a login to access like email accounts, banking portals, and subscription services. And (c) is the dark web, which is the part of the deep web that isn’t indexed by search engines and requires special tools like Tor Browser to access. The darknet version of DuckDuckGo is not a search engine for the dark web, but a private browsing tool for the dark web. DuckDuckGo’s regular site can take you to the dark web, as it brings up onion sites and dark web links when searched.
SimplyTranslate is an onion based language translation service using the google translate engine. It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web. However, this does not provide any extra security for your device or information.
In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. For instance, if you want to buy a laptop or a smartphone, you can try your luck in one of these shops. Sure, you can use other cryptocurrencies if Bitcoin’s not your cup of tea. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN.


