VPN provides another degree of protection and allows you to access Dark Web connections that may be blocked in your location. NordVPN is your best chance for safely accessing the Dark Web, thanks to customer controls and solid security. It is crucial to emphasize, however, that the Dark Web may be dangerous, and even with NordVPN, vigilance should be constant in order to avoid frauds and criminal activity.
Cybersecurity Blogs And Forums
The Silk Road left a lasting legacy, influencing the emergence of numerous other darknet markets, and igniting ongoing debates surrounding privacy, ethics, and the regulation of online spaces. Before entering the Dark Web, it is crucial to educate you with Darknet markets. These internet markets facilitate the buy and sell of unlawful items and services, like narcotics, stolen data, and black money.
Can I Access The Dark Web With The Tor Browser?
The FBI, DEA and international partners infiltrated the site during Operation Bayonet. On July 5, 2017, Thai police arrested founder Alexandre Cazes; a week later he was found dead in his Bangkok cell. Authorities seized AlphaBay’s servers and cryptocurrency wallets, replacing the homepage with a seizure banner and simultaneously taking over the rival Hansa Market to harvest user data. Operational security, or OPSEC, is the discipline that turns technical anonymity into real‑world protection. Tor and VPNs mask your network path, but a single careless click can still expose your identity. Follow these best practices every time you venture onto the dark web.
The Ultimate 2025 Guide To The Tor Browser
Setting up the Tor and VPN separately is recommended if this is a concern. If you want privacy and anonymity, NordVPN accepts payment in Bitcoin. Moreover, it offers a 24/7 customer support service and a 30-day money-back guarantee. Some people would argue about its reliability because they claim it’s watched. Still, download the Tor browser from its official website only and nowhere else so your computer doesn’t get any spyware or malware. Purchases through links on our pages may yield affiliate revenue for us.
Following Dream Market’s closure, users started looking for alternatives. While no single platform has fully replaced it, several dark web markets have gained attention. These sites aim to provide the same level of security and ease of use, but users are still cautious due to the risks of law enforcement activity. Some alternatives links to different markets in 2024 can be found by visiting our Darknet Market Links Directory. You can legally browse darknet sites for legitimate purposes like research or privacy protection. However, engaging in illegal activities on the darknet is against the law and can result in serious criminal charges.
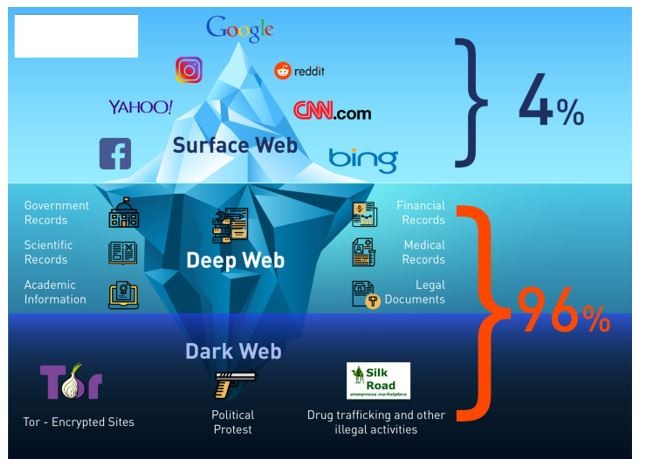
What Is The Difference Between The Dark, Deep, And Surface Web?
Many of these markets operate internationally, and some have certain specialties. DNMs have a limited life and may be shutdown suddenly, leaving users with unfulfilled orders and sellers with no means of communication. DNMs may start when a single person, or a small group of people, decide to build one.
Hidden services are exclusive to the Tor network, identified by domain names ending in .onion. They are not indexed by public search engines, and access requires knowing the specific address. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. Accessing the Dark Web can expose you to a range of risks that might not be immediately apparent.
It is also available on various operating systems, including Linux, Windows, MacOS, iOS, and Android. However, it’s important to note that NordVPN can see your traffic details before encrypting them, even though it does not keep logs. A VPN helps you browse the web more securely and privately by adding an extra layer of encryption to your data. However, not all VPNs are reliable, and some may collect your personal information while others slow you down. If you are curious about accessing the deep web, you are likely already using it daily through pending website redesigns, blog posts under review, and pages accessed during online banking.
I2P is an anonymous overlay network designed primarily for peer-to-peer applications. It’s no longer news to you that the Tor browser is how you get inside the dark web, but that’s not all this powerful browser does. Tor browser also offers a level of online security and anonymity that you can’t get from regular browsers like Chrome or Safari. Essentially, a VPN provides you with robust online security to avoid threats to your privacy. But the question is, with so many services, which one is the best among them? Well, we have been providing our users with in-depth analysis about VPNs and other privacy tools.

Method II – VPN Over Tor
Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you.
Dream Market V2
- It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself.
- Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks.
- The same goes for the different pages that pop up in webmail services, like Gmail, or academic databases on a university network.
- Always remember that the dark web is a people-centric community.
The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection. The Dark Web is a section of the Internet that isn’t searched for by search engines and can only be accessed with specific software, setups and dark web search engine.

Should I Only Use A VPN To Access The Dark Web?
Some of these cybercriminals are known to track and blackmail pedophiles. Moreover, hackers who offer their services over the dark web have also targeted financial institutions and banks. Fraudulent activities on the dark web include phishing scams, fake identity sales, and the sale of fake products.
What makes this market popular is the fact that it’s less expensive compared to the rest. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You should also consider freezing your credit to prevent identity theft. This can be stopped if law enforcement agencies can break any link, particularly dark web marketplaces, in the chain.
Traffic logs are a bigger concern than session logs, but neither are good. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions. If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details.