In fact, WeTheNorth is more of a private club than an open market – something its operators want. Every potential participant’s credentials must be vigorously vetted before they can join. That way, they aim to create secure forums and limit outsiders like law enforcement. Likewise, law enforcement agencies each day continue to fine-tune their strategies to get past these networks. There are some things that you can’t find on the surface internet but are available in the darknet markets. Therefore, it’s almost impossible for authorities to track those who run the darknet markets or even their locations.

Best Darknet Markets
XMR hides transaction details, unlike BTC, which dropped 40% in use due to tracking risks since 2023. We’re back with another video in our Webz Insider video series on everything web data. Abacus’s exit follows the June 16, 2025 law enforcement seizure of Archetyp Market, marking the latest in a series of shutdowns in the Western DNM ecosystem.
Making Cybercrime Easy For Anyone
A data breach can also occur accidentally, for example if someone’s login credentials are accidentally published. Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero. Abacus alone represented nearly 5 per cent of total DNM revenue, underscoring the ongoing scale of underground commerce.
Drughub Darknet Market
Such companies’ tools enable investigators to trace administrator wallets and follow illicit flows even after a marketplace goes offline. Even as major darknet platforms fall, TRM Labs data shows that the ecosystem remains highly adaptive. Following the 2022 shutdown of Hydra Market, TRM identified new Russian-language darknet markets emerging that by 2024 accounted for more than 97% of global darknet drug revenues.

Acronis Cyber Protect Cloud: New Version C2505
The Tor browser is a special web browser that allows users to access the darknet cc market and other hidden services on the internet. It works by routing internet traffic through a network of servers, which helps to hide the user’s IP address and location. Taking these steps cannot eliminate all risks (exit scams and law enforcement still happen), but they significantly improve privacy and security when researching dark web markets. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data.
Did Abacus’s Success Lead To Its Closure?
KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. Always use a fake name and a temporary email address when you buy something from the dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web.
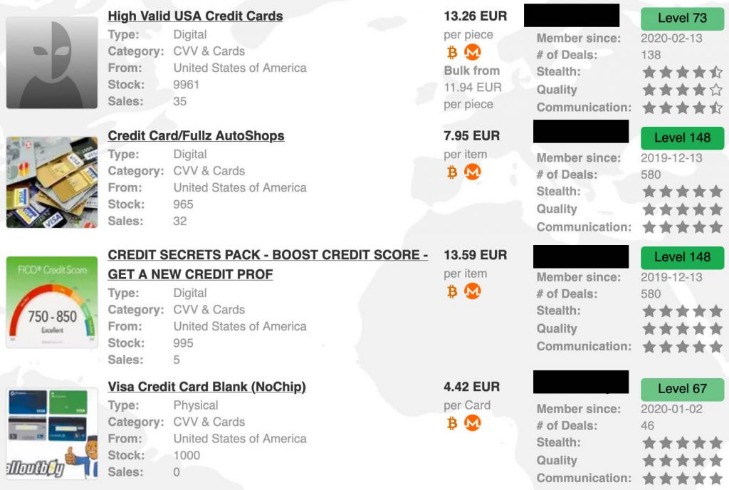
The darknet CC market is a bustling online marketplace where users can buy and sell stolen credit card information. While the concept may seem shady, it’s important to understand that this type of market exists and how it operates in order to protect yourself from becoming a victim. Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering.
Matrix Darknet Search Engine
The use of Tor and other privacy-focused tools ensures that users can access these platforms without compromising their anonymity. As the darknet ecosystem evolves, it continues to adapt to user needs, offering a reliable and secure environment for trade. The demand for pharmaceuticals on darknet markets remains high, with a focus on prescription medications, nootropics, and performance-enhancing drugs. These products are often sourced from international suppliers, ensuring competitive pricing and a wide variety of options.
What Is The Main Product Sold In The Darknet CC Market?
- Adopting simple rules and habits, such as using different passwords for different accounts and employing a password manager, can help keep personal data out of the reach of cybercriminals.
- Financial institutions also suffer immense losses due to fraudulent transactions, often passing these costs onto consumers through increased fees and interest rates.
- When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track.
- Additionally, the growing popularity of darknet forums and magazines has created a robust ecosystem where users can share reviews, discuss trends, and stay updated on new market links.
This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. To do this, we first identified 30 darknet markets advertising stolen data products. It is common to hear news reports about large data breaches, but what happens once your personal data is stolen? Our research shows that, like most legal commodities, stolen data products flow through a supply chain consisting of producers, wholesalers, and consumers.
Some alternative links are available, providing access to the marketplace. It’s recommended not to use new alternative links as they could just be planned exit scams. Thanks to torzon mirror, I’ve discovered a whole new world of torzon market possibilities. The innovative tools, inspiring content, and supportive community have empowered me to explore my creativity and take my torzon darknet skills to new heights. The wethenorth shop provides detailed educational materials and wethenorth tor access tutorials for new participants. Built-in protection mechanisms within the wethenorth darknet shop system actively counter security threats.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
The platform’s user feedback system allows buyers to make informed decisions, while its integrated dispute resolution mechanism ensures fair outcomes in case of disagreements. One of the most notable markets is PhantomX, which has gained popularity for its robust escrow system and multi-signature wallet integration. This ensures that funds are only released once both parties confirm the transaction, significantly reducing the risk of fraud. Additionally, PhantomX employs a decentralized hosting model, making it resistant to takedowns and ensuring continuous availability. If you believe your credit card information has been compromised, contact your credit card company immediately. You should also consider placing a fraud alert on your credit report to prevent further unauthorized use of your information.
The dark web is famous when it comes to hosting as well as spreading explicit and illegal content. It is home to all sorts of disturbing content, given that the markets share content related to non-consensual recordings and child exploitation. Interestingly, the hackers don’t hide, but most of them even openly advertise what they offer on the darknet forums. Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts. The darknet is basically an overlay network that exists within the internet and can only be accessed with specific configurations, software, and usually uses certain customized communication protocols.

