Once you do, that provider will need to configure the entire thing on a specific server first. This server will route your Tor traffic and perform what you want. This method is far more complex but we’ll still explain it for those too curious. As opposed to the previous situation, here, you’re first connecting to Tor and then the VPN.
H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Before you embark on your journey into the Dark Web, it’s crucial to establish a secure foundation. While the Tor network is designed to provide anonymity, it alone cannot guarantee your privacy or safety. This section will guide you through the essential preparatory steps and tools to ensure that you remain as protected as possible while exploring hidden services and tor onion domains.
What Is The Dark Web? Myths, Realities And Cybersecurity Risks
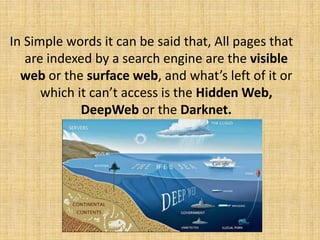
Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses. Search engines like Google, Bing, and Yahoo can access just about 4% of the web. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
Should I Only Use A VPN To Access The Dark Web?
While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. The darknet is often considered a hidden part of the internet, where data and information are inaccessible to ordinary users. On the other hand, Tor (short for The Onion Router) is software that allows access to the Darknet through a layered encryption system known as onion routing. The technology focuses not only on anonymity but also on freedom of expression, especially in countries with strict censorship.
- Facebook offers an onion link to access their services, although you may find logging in difficult, as you’ll most likely appear to be signing in from a different location each time.
- It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security.
- Below are details on how to set up key tools for accessing and using the darknet securely.
- To look at it in a different way, it makes up between 90% and 95% of the internet.
- As your traffic passes through Tor, it’s encrypted and bounced between at least three relay points, known as nodes.
- What we see and use on the internet in web browsers such as Edge, Chrome, Firefox, Opera, and Safari is only a fraction of what is actually available.
Sections of the dark web are often closed down too, as part of police operations. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI.

Use NordVPN For Maximum Security
Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship. With Tor Browser, you are free to access sites your home network may have blocked. Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. Tails is a mere 1.3 GB download, so on most connections it will download quickly. You can install it on any USB stick that has at least 8 GB of space.
Cybersecurity Course Fees A Complete Guide To Costs, Certifications
The dark web is a decentralized web, which means that the data is stored on many different servers around the world. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. The release of Freenet in 2000 is considered by many as the start or founding of the dark web.

Are Dark Websites Illegal To Use And Visit?
Darknet markets facilitate transactions for illegal goods and services. Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources. While many dark marketplaces have been shut down by authorities, new ones soon appear in their place.
Risks And Dangers Of The Dark Web
These legitimate media companies keep a presence on the dark web to help users who might, for a variety of reasons, have difficulty accessing their content on the open web. Encrypted communication channels on the dark web allow users to message back and forth in an anonymous online environment. However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely. The dark web is a hidden part of the web that carries several illegal activities, including drug and weapon dealing, pornography, private data, and more. But, this isn’t only about bad things; you can also get useful information.
Https://g7ejphhubv5idbbu3hb3wawrs5adw7tkx7yjabnf65xtzztgg4hcsqqdonion/
- I2P, or the Invisible Internet Project, is an anonymous network layer to facilitate secure and private communication among its users.
- In the internet’s darkest corners, a myriad of hidden websites cater to an array of needs and interests.
- Once you’ve securely connected to the Dark Web via Tor, the next step is locating legitimate .onion sites.
- The most common darknet software is the free and open-source Tor, short for the Onion Router.
The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there.
However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet.
Is The Dark Web Used For Illegal Purposes?
Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. Exodus Marketplace started to become popular after the shutdown of Genesis Market, and it replaced it successfully.
It also provides a safe haven for whistleblowers, journalists and those seeking free expression under oppressive regimes. A combination of specific tools allows users to access the darknet and navigate hidden pages that traditional search engines like Google or Bing can’t reach while staying anonymous. That may seem an extreme way to browse the web, but such protections are increasingly worth considering, says Sarah Jamie Lewis, executive director of the Open Privacy Research Society. If you exercise due caution and use a combination of the Tor browser and common sense in which sites you access on the dark web, yes, the dark web is safe to use. You may be targeted by law enforcement, exploited by hackers, or threatened by criminals using the dark web for nefarious purposes. The following sections will explain how to access the dark web on different devices.
Being the unregulated part of the internet, the dark web is full of illegal activities. The chances of opening websites with malicious, inappropriate, or illegal content are very high, especially if you don’t know the exact .onion website you wish to visit. There is a significant risk that the government can target you for visiting a dark website, as many Tor-based sites have been taken over by police authorities worldwide. Even if a person does not make any purchases on illegal marketplaces like the Silk Road, custom software used by law officials can analyze activity and identify user identities. This is below the surface web and accounts for about 90% of all websites.