Legitimate organizations and companies also sometimes establish a presence on the dark web. Law enforcement agencies monitor the dark web for stolen data and criminal activity, while major media organizations track whistleblowing sites for news. The second layer of the internet, also known as the Deep Web, exists just below the Surface Web. The deep web contains regular websites which authorized users can only access. The deep web is hidden from plain view, but most internet dwells in this layer.
Best Anonymous Dark Web Browsers On The Tor Network
The “surface web” constitutes the portion indexed by standard search engines like Google and Bing, readily accessible to the average user. Beneath this lies the “deep web,” a significantly larger segment encompassing content not indexed by these search engines. This includes resources requiring specific credentials or access, such as online banking portals, private databases, and academic journals.
- These tunnels are identified by requiring the same over a network database, which is more of a structured distributed hash table based on the Kademelia algorithm.
- The safest and best dark web browsing tool for Android users is the official Tor Browser APK from the Tor Project site.
- We recommend that you use only the Tor browser to access the deep, dark web, if you must.
- The US Supreme Court has indicated that even casual browsing could lead to legal consequences.
- Using a VPN in conjunction with the Tor Browser is an excellent way to keep your online travels secure and private.
- This cryptographic basis ensures that the address is directly linked to the service’s identity within the Tor network.
WANT TO TRY THE TOP TOR VPN RISK FREE?
So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful. Tor Browser already comes with HTTPS Everywhere, NoScript, and other patches to protect your privacy and security. Tor Browser is supported on any modern Linux-based operating system.
What Is The Best VPN For Tor?
Besides the possible criminal elements you may encounter, hackers and malware are rampant. In fact, generally it is wise to simply not venture into the dark web in the first place. Few people have good reasons to take such risks, though some in the fields of law enforcement or cybersecurity are exceptions. Still, if you’re determined to do some exploring, there are ways to minimize your risks.
Https://g7ejphhubv5idbbu3hb3wawrs5adw7tkx7yjabnf65xtzztgg4hcsqqdonion/
In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
How To Download And Use Tor
Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. It is an excellent option if you want to surf the web anonymously. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions.
De-anonymization And Surveillance
When accessing the dark web, using specialized browsers alone isn’t enough. Here’s a practical overview of the most essential tools available in 2025. One of the most significant dangers is the high likelihood of encountering malware, ransomware, and other forms of malicious software. The dark web serves as a common platform for cybercriminals to distribute various types of malicious software designed to compromise users’ devices and steal their personal information.
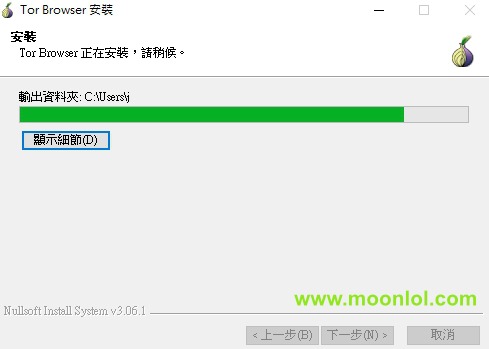
Step 3: Install And Launch Tor
The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article). Though people usually think of dark websites as the wrong online place, that’s not the complete truth. Although the underground internet world is rife with everything bad, it also hosts positive elements. It then depends on you, as the user, how you surf the dark world. Tor Browser masks your IP address and routes traffic through multiple servers.
DuckDuckGo, known for its privacy-focused approach on the surface web, also has a presence on the dark web. DuckDuckGo does not track your search history or collect personal data, making it a strong privacy-preserving option for searching both the surface and dark web. Exploring the dark web can be a fascinating journey, but it requires the right tools and safety precautions.

And that’s no coincidence—it’s the most popular and trusted browser for exploring this hidden part of the internet. Tor greatly enhances anonymity, but if an attacker controls both the entry and exit nodes, they could attempt traffic correlation to link your identity to your activity. You can also be tracked by logging into personal accounts, downloading unsafe files, or modifying browser settings that expose your digital fingerprint. Using Tor with a VPN adds an extra layer of protection by masking your IP from the Tor entry node. You’ll need a specialized dark web browser like Tor, which lets you access hidden parts of the internet while protecting your identity. Tor works by routing your traffic through multiple encrypted servers, masking your location, and making it much harder to track your online activity.
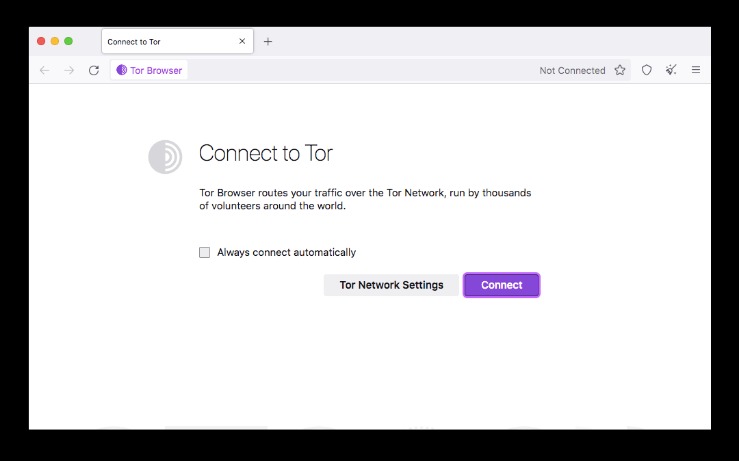
How To Set Up And Use Tor For The First Time
Tor is an effective and easy-to-use tool for people worried about online anonymity and privacy. Its clean and uncomplicated interface is straightforward to navigate, allowing you to easily toggle between anonymous and non-anonymous browsing. The tool is light on system resources and doesn’t affect computer performance.
Accessing Hidden Services

We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention. If you find that Tor is restricted in your current location, you can use a bridge. A bridge creates an obfuscated relay on the Tor network that is not listed in the main directory. That means that even if an ISP is monitoring all of the known Tor relays, they may not be able to block all of the obfuscated bridges. This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels.
- Preventive Approach participates in various affiliate marketing programs, which means we may get paid commissions on editorially chosen products purchased through our links to retailer sites.
- Practice safe, smart digital habits if you must use Tor to log into personal accounts.
- These sites are only accessible over the Tor network and are commonly used for privacy and anonymity.
- The Tor browser is designed to provide improved online anonymity and security.
- Tor’s encryption tries to keep your identity and destination secret, but bad actors can still find a way to identify you.
- Furthermore, it uses a multi-layer build, which increases the security level regarding your privacy and anonymity.
With TecnetOne, you see what others don’t—and act before it’s too late. It can take a little while to load and it’s not as intuitive as other systems. But if you’re serious about maximum privacy, it’s absolutely worth the effort. It’s ideal for journalists, activists, or anyone who needs to browse without leaving digital footprints. And yes, it also works perfectly for those who just want to explore the dark web with peace of mind. What truly sets Freenet apart is its radical stance on information freedom.