We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
Risks Of Accessing The Dark Web:
Furthermore, the VPN offers a dedicated dark web feature called Dark Web Monitoring that alerts you if your privacy has been breached or some of your login credentials are available on it. Orbot is free, open source, and can even replace your VPN, if you don’t mind slower browsing speeds. Remember that activity within apps you’re logged into will be recorded, even if you’re using Tor. While not a browser itself, Orbot can encrypt traffic from your mobile browser, Gmail app, Google Maps, instant messaging apps, etc., using the Tor protocol.
Search engines index all the web resources on the surface web, so you can search for them online. You just need standard browsers like Chrome, Edge, and Safari to open websites on the surface web. These search engines prioritize privacy and often index websites that aren’t listed on the surface web. Keep in mind that the dark web can be unpredictable, and search engines may not always yield comprehensive results.

Navigating The Dark Web Safely
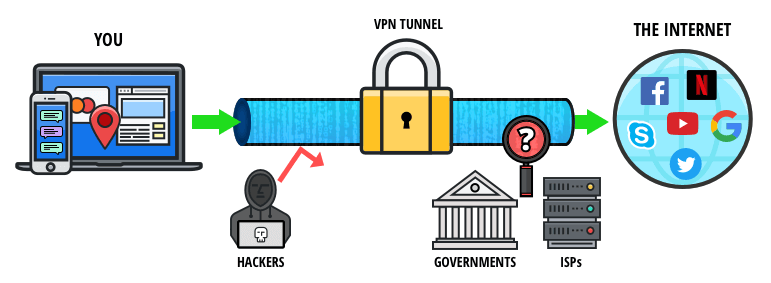
Tor can be used together with a VPN to provide overlapping layers of privacy and anonymity. The dark internet is designed to provide anonymity by keeping communication private through encryption and routing online content through multiple web servers. While the dark web is often depicted as an anarchic forum for criminal activity, that’s not necessarily true. The darknet is simply an anonymous space on the web that can be abused or appreciated in turn. Using a virtual private network (VPN) is a crucial first step before diving into the dark web.
- This is where Tor websites are located, deemed the ‘dark web,’ and can only be accessed by an anonymous browser.
- Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously).
- However, some of these alleged services, such as professional ‘hitmen,’ may be scams designed to defraud willing customers.
- As long as users take the necessary precautions, no one knows who anyone else is in the real world.
- Chill, because nobody will ever find a record of you ever fiddling around the darknet.
Thus for every page publicly available on Tech Advisor (and there are literally millions), there is another on the Deep Web. The first step is to download and configure the Tor browser from its official website. The Tor browser is your gateway to the dark web, allowing you to access .onion sites anonymously. The deep web includes non-indexed databases and private portals, while the dark web specifically requires Tor and includes .onion sites. Accessing the dark web is legal in India as long as you do not engage in illegal activities such as buying drugs or hacking services. As mentioned earlier, many websites consider Tor suspicious and block users entirely.
Secure Account Management And Communication
While it offers unparalleled privacy and freedom, it also requires vigilance and caution. By understanding its structure and ensuring safe browsing practices with tools like Forest VPN, we can navigate this digital underbelly responsibly. Whether you’re exploring for curiosity or necessity, the dark web reminds us of the dual nature of technology—empowering yet enigmatic. Opting for Forest VPN ensures your privacy remains intact while browsing the dark web. With its no-log policy and battery-saving technology, Forest VPN not only protects your data but also minimizes your carbon footprint.
Safe Browsing Tips:
Importantly, each node is representative of an additional layer of encryption. No node can track the complete path the traffic has taken, and more importantly, neither can anyone who finds it on the other side. Only the entry node can view your IP address (more on how to stop this happening later).
- There is only one official download site for the Tor browser, and that is torproject.org.
- Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy.
- Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences.
- Nevertheless, caution should always be exercised when venturing into this hidden realm.
Commercial Services
Always use an abundance of caution when interacting with anything or anyone on the dark web. Founded in 2013, the site’s mission is to help users around the world reclaim their right to privacy. Freelancing alongside these roles, his work has appeared in publications such as Vice, Metro, Tablet and New Internationalist, as well as The Week’s online edition. Deep down, the tip of the iceberg is where over 90% of the internet content is. As much as the dark web is supposed to promote free speech alongside bypassing censorship, many shady activities occur there. Also, your data is more likely on the deep internet in one way or the other.
How To Browse The Dark Web Legally & Safely?
Conversely, the Darknet mode allows you to create restricted anonymity networks of people you only trust or know to share content with. The Virtual Private Network offers over 3,000 servers distributed across 105 countries globally. Its impressive connection speed minimizes buffering while browsing the dark web.
The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors.
Its main appeal is that it offers more privacy and supports legacy Firefox add-ons. It also eliminates data collection, telemetry, and other suspicious code modern web browsers tend to use, which are troubling at best. It is made up of two virtual machines – a Gateway and a Workstation.

But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). Typically, any reference to the visible web will be to common websites with a familiar internet domain extension.
The “Dark Web” often conjures up images of hidden marketplaces, illicit trades, and shadowy figures lurking in the digital underworld. The Dark Web is simply a part of the internet that cannot be reached by standard search engines and browsers. While it’s true that some corners harbor illegal activities, it also provides a platform for whistleblowers, journalists, activists, and everyday users seeking privacy and freedom from censorship. That may seem an extreme way to browse the web, but such protections are increasingly worth considering, says Sarah Jamie Lewis, executive director of the Open Privacy Research Society. Dark web browsers rely on complex encryption protocols to route users’ connections through multiple servers, making it nearly impossible to trace activity back to the original user. Most dark web browsers use The Onion Routing (Tor) network, where data is encrypted in layers and sent through multiple nodes.


