To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. The Hydra listing shown above advertises a service, where in return for a cryptocurrency payment, the vendor will bury bales of vacuum-packed physical cash “5-20 cm under the ground”.
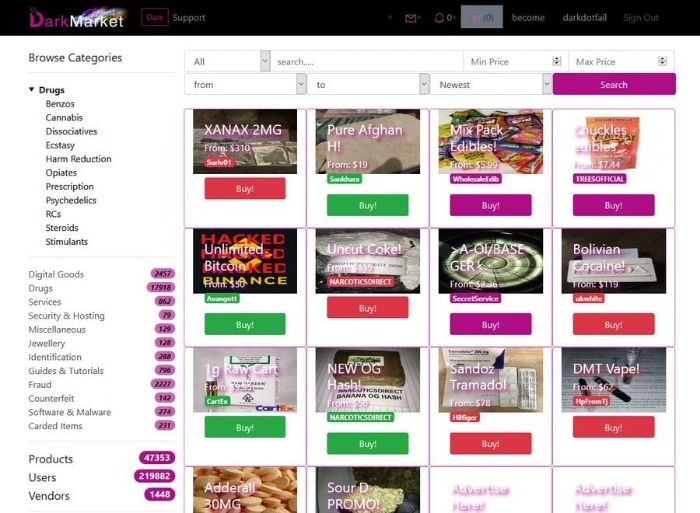
A Step-by-Step Guide To Buying On The Darknet
Threat reports consistently rank it among the top ten darknet sites Top 10 Dark Web Markets. According to Chainalysis, the total number of active markets in November 2020 (37) is the lowest total seen since November 2017. Consequently, the darknet market industry has consolidated to a smaller number of bigger players.
- Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025.
- Of course, someone writing about how crypto still is or isn’t used for illicit purposes widely doesn’t do much without hard data.
- Among the 40 large DWMs under consideration, 17 participate in at least one transaction in either 2020 or 2021, while the remaining 23 closed before 2020.
- In the below graph, the currencies included are Bitcoin, Bitcoin Cash, Litecoin, and Tether.
- Similarly, there is no unique choice for the classification parameters or ground truth for fitting them.
The Dark Side Of Cryptocurrency: How Digital Assets Fuel Money Laundering And Illicit Trades
We reveal that stable U2U pairs play a crucial role for marketplaces by spending significantly more time and generating far greater transaction volume with DWMs than other users. By analysing the temporal evolution of stable pairs, we unveil that DWMs acted as meeting points for 37,192 users (out of around 16 million), whose trading volume is estimated to be $417 million. Importantly, these newly formed stable pairs persist over time and transact for several months even after the closure of the DWM that spurred their formation. Finally, we observe that COVID-19 only had a temporary impact on the evolution of stable U2U pairs, which continued to increase their trading volume throughout 2020.
Stealth Addresses

And while the number of markets appears to be on the decline, those that remain are making more money than ever before. Cryptocurrency is commonly used on darknet markets due to its perceived anonymity and its ease and efficiency for transferring funds across international borders. This prosecution is part of an Organized Crime Drug Enforcement Task Force (OCDETF) investigation. Our classification shows that the number of sellers is significantly smaller than the number of buyers, as shown in Figs. The number of actors in the ecosystem is affected by several factors, especially market closures. Notably, the number of buyers and sellers significantly drops after the operation Bayonet in the last quarter of 2017, which shut down AlphaBay and Hansa markets, causing a major shock in the ecosystem34.

To find out which darknet markets are currently popular, and the .onion URL required to visit each one, see Darknetlive.com or dark.fail. Dark.fail lists numerous darknet sites, including forums; scroll down the page until you see the names of darknet markets and look for the green light beside the URL to denote that it’s currently online. The seller will check their account and, when they see the funds, release the bitcoin that’s locked in the escrow wallet.
Silk Road Was The Darknet Market Testing Ground For Bitcoin
On average, marketplaces had 109 unique vendor aliases and 3,222 product listings related to stolen data products. Marketplaces recorded 632,207 sales across these markets, which generated $140,337,999 in total revenue. On average, marketplaces had 26,342 sales and generated $5,847,417 in revenue. It is common to hear news reports about large data breaches, but what happens once your personal data is stolen? Our research shows that, like most legal commodities, stolen data products flow through a supply chain consisting of producers, wholesalers, and consumers. But this supply chain involves the interconnection of multiple criminal organizations operating in illicit underground marketplaces.
Top 7 Dark Web Marketplaces
N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools.
About This Article
Cryptocurrencies, especially Bitcoin and Monero, are commonly used for ransom payments due to their pseudonymity and global reach. While Bitcoin’s transparent ledger aids forensic investigations, Monero’s privacy features make tracing transactions difficult. In response, governments are enhancing blockchain surveillance and enforcing stricter regulations to combat crypto-enabled cybercrime. Criminals employ layering and structuring methods to conceal their illicit Bitcoin transactions, which are hard to track and regulate. By breaking large sums into smaller transfers and leveraging multiple exchanges, they evade regulatory scrutiny.
Despite restrictions, the demand for anonymity and privacy persists, and developer communities continue to seek innovative solutions to maintain these values. Despite current difficulties, projects like Monero remain active due to committed communities and continuous technical growth aimed at improving privacy and security. Privacy cryptocurrencies are not only for illicit purposes but also represent a paradigm for protecting financial privacy in an increasingly monitored world. Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem.

2a, where the overall ecosystem volume quickly recovers after market closures. This is an outcome of the ecosystem’s resilience, largely supported by the migration of users15. Correspondingly, the multihoming activity is a mechanism that contributes to the ecosystem’s resilience. Because they are already active in more than one market, the migration cost for the multihomers is usually smaller compared to that for non-multihomer users, especially for sellers, that need to rebuilt their reputation23. The rise of NFTs and DeFi platforms has introduced new financial opportunities but also significant risks. Money laundering through NFTs thrives on anonymity and subjective pricing, making it difficult to track illicit transactions.
For instance, the receiver needs to provide his “channel point” when creating an invoice. A channel point is the UTXO on the blockchain that is used to back the channel with on-chain bitcoin; that means that the sender can view the receiver’s on-chain transaction history. A CoinJoin is a collaborative transaction that combines users’ coins in order to create a large anonymity set for them. Those have multiple flaws and massive third-party risks, and they are also often honeypots set up by law enforcement to catch dirty bitcoin and surveil on users. Darknet markets, perpetually in flux, are seeing Bitcoin regain prominence due to regulatory restrictions on privacy coins.
We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc. Although other coins are used, such as Monero recently, Bitcoin is still the mostly used in the ecosystem, being supported by more than 93% of markets7,9. The pre-processing relies on established state-of-the-art heuristics to cluster addresses into entities, such as cospending, intelligence-base, and behavioral clustering39,40,41,42. The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction.

Stolen Data Ecosystem
The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation.