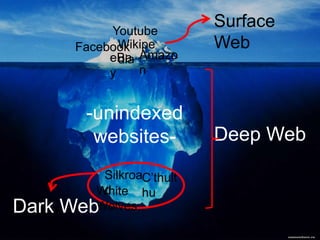
Veridian aims to provide a single portal to all the historical newspapers of the world. It’s a fantastic resource for researchers—especially family historians, genealogists, and students. Use platforms like Dark.fail or Onion.live to check uptime, domain authenticity, and community trust levels before accessing a dark web site. Yes, platforms like DeHashed, LeakLooker, and DeepPaste provide access to data breaches and leaked credentials. OSINT professionals must venture where conventional tools can’t reach—and the dark web is one such frontier.
Directory Of Open Access Journals
- However, keep in mind that the Tor browser is not officially available for both of these platforms.
- Even the regular search engine offers more deep web content than Google.
- Articles are published regularly and include interesting information, images, and quotes from officials.
- If you’ve ever experienced an uptick in phishing attacks and spam after a data leak or breach, it may be because your personal information has been posted to the dark web.
It describes itself as a tool for social change and “a project to create democratic alternatives.” Riseup requires you to have the onion link as well as an invitation. SecureDrop uses Tor to provide a safe way for whistleblowers to contact various news outlets. Prominent organizations like The Guardian, The New York Times, and ProPublica have implemented it. The software requires two-factor authentication to receive what’s been uploaded by the whistleblower and allows two-way communication between the anonymous contact and the media outlet.
The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
PRIVACY ALERT: Websites You Visit Can Find Out Who You Are
However, it works best in real-time since the file transfers are interrupted if you turn off your system. Just remember that this is a Dark Web resource, which means that much of the content is likely in breach of copyright. That said, it is one of the most famous and popular Dark Web sites, and it does have legitimate uses. For instance, in the UK, any book older than 70 years old (past the date of the author’s death) is no longer subject to copyright restrictions. This means you can safely download older manuscripts and other public domain works.
And because they aren’t searchable via Google or Bing, onion site lists are important roadmaps to help users find what they’re looking for on the dark web. The dark web hosts a wide range of sites — from whistleblower tools and secure email platforms to underground forums, black markets, and dark web mirrors of legitimate news outlets. A VPN protects your connection against everyone, not just your ISP and the authorities. It encrypts your connection to prevent outsiders from being able to read your data and masks your IP address with one from a VPN server—so whoever’s looking can’t get any useful information. This process also prevents your ISP from seeing your data or where it’s going.
Invictus Market
It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. Viney Dhiman, the mind behind GeekerMag, is a seasoned content writer with over 12 years of experience. Specializing in simplifying complex tech concepts, he covers Windows OS, Android, iOS, web apps, and product reviews.
New Shamos Malware On Mac: Beware Of ClickFix Attacks

Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. Changing the Tor browser settings can further boost your security levels on the dark web shops. For instance, you can choose the preferred security levels for enhanced protection. The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web.
Related Articles From The Safe Browsing Section
Sadly, one of the most famous deep search engines from the past, Deeppeep, no longer exists, but all the sites in the article can help to recreate the lost features. Unlike Google, Pipl can interact with searchable databases, member directories, court records, and other deep internet search content to offer you a detailed snapshot of a person. No, many .onion sites serve legal and ethical purposes such as secure communications, anonymous sharing, and journalism support. Yes, OnionLand is a dark web search engine that allows you to search through forums and other hidden .onion content. Yes, the Hidden Wiki remains one of the most accessed community-curated directories for .onion links, though users must verify each link’s authenticity.

II Security And Anonymity On The Dark Web
Some examples include human trafficking, drug trade, weapons dealing, and pornography, to name a few. The dark web, on the other hand, is defined as the subdivision of the deep web. The bad reputation of the latter stems from its association to the dark web, where much of the illegal activities on the Internet takes place. First, visit torproject.org and download the software for your device. If you are using an iPhone or iPad, download the Onion Browser instead since there is no iOS version of Tor. Its accessibility and variety of fraud tools make it a valuable resource for low- to mid-tier threat actors.
One of its best features is Anonymous View, which is a free proxy that masks your identity while you’re browsing sites. It also always uses a secure HTTPS connection, so you’re safer on public Wi-Fi networks too. DuckDuckGo also lets you access chatbots anonymously, has image, video, news, shopping, and other search options.
- If this sounds similar to The Wayback Machine, the concept is indeed the same.
- This platform provides a sanctuary for users to connect, share insights, and engage in discussions without the constraints of mainstream platforms.
- These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access.
- Onion sites are websites on the dark web that use the “.onion” top-level domain instead of “.com,” “.net,” “.gov,” etc.
- Riseup is available on the surface web, but its presence on the Tor network extends its privacy benefits by letting you use its services without exposing their real-world identities.
Stay Safe On Dark Web Websites
His work can be found on popular tech websites like Gizmodo and The Verge, and he has been interviewed by the Microsoft Edge team. The Dark Web has a notorious reputation for hosting a platform for criminal and evil activities. While many of the scary stories you might have heard be true, many people surf the dark web for innocuous purposes. Privacy advocates frown upon it because of the way it harvests data and profiles users.
Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. To stay safe on the dark web, use a VPN to mask your IP address, avoid clicking on unfamiliar links, and never enter personal information. It’s also advisable to use antivirus software to protect against malware.


